In an era of escalating cyber threats, trust UrbanTech to safeguard your digital world.
Our comprehensive Cyber Security Services fortify your defenses, protect your data, and ensure your peace of mind.
Vulnerability Assessment
Identify weaknesses before cyber threats do. Our expert Vulnerability Assessment Services provide a thorough examination of your digital infrastructure, fortifying your defenses and preserving your security
Email Security
Defend your digital communication with UrbanTech's Email Security Services. We provide robust solutions to shield your emails from cyber threats, ensuring confidentiality and integrity.
ISO27001 Implementation
Organizations must design and implement their Information Security Framework in accordance with an auditable standard. UrbanTech guide you through the implementation process, ensuring robust security measures and compliance.
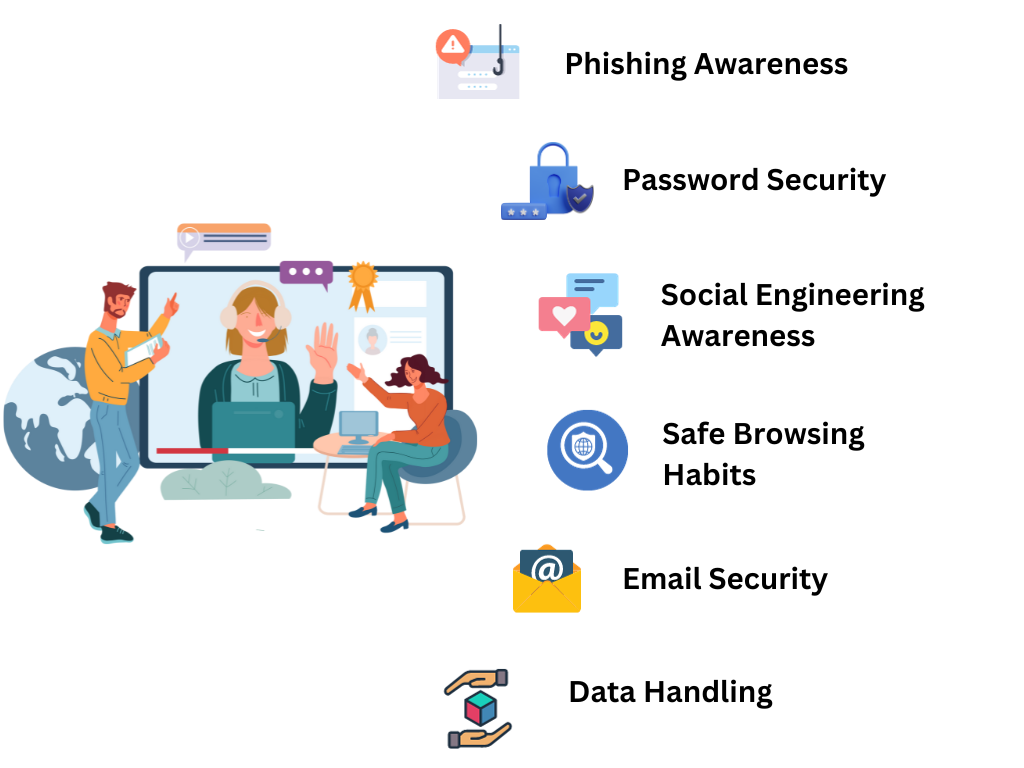
Security Awareness Training
Your workforce is your first line of defense against cyber threats. Our Security Awareness Training equips your team with knowledge and skills to safeguard your organization.
Stay one step ahead of cyber-attacks with our proactive Cybersecurity Services.
FAQs
A vulnerability assessment identifies weaknesses in systems, applications, and networks to proactively address potential security risks and enhance overall cybersecurity.
Email is a common vector for cyber threats. Proper email security measures protect against phishing, malware, and unauthorized access, safeguarding sensitive information.
ISO 27001 is an international standard for information security management systems, providing a systematic approach to managing sensitive information and ensuring its confidentiality, integrity, and availability.
Certification demonstrates a commitment to information security, boosts customer confidence, and provides a framework for continuous improvement in managing security risks.
Training would cover password security, phishing awareness, device security, data protection, and the organization's specific cybersecurity policies and procedures.